AI Agent Identity & OAuth Grant Exposure Check
Find out in under 4 minutes whether AI agents are running on governed identities or hidden OAuth grants.
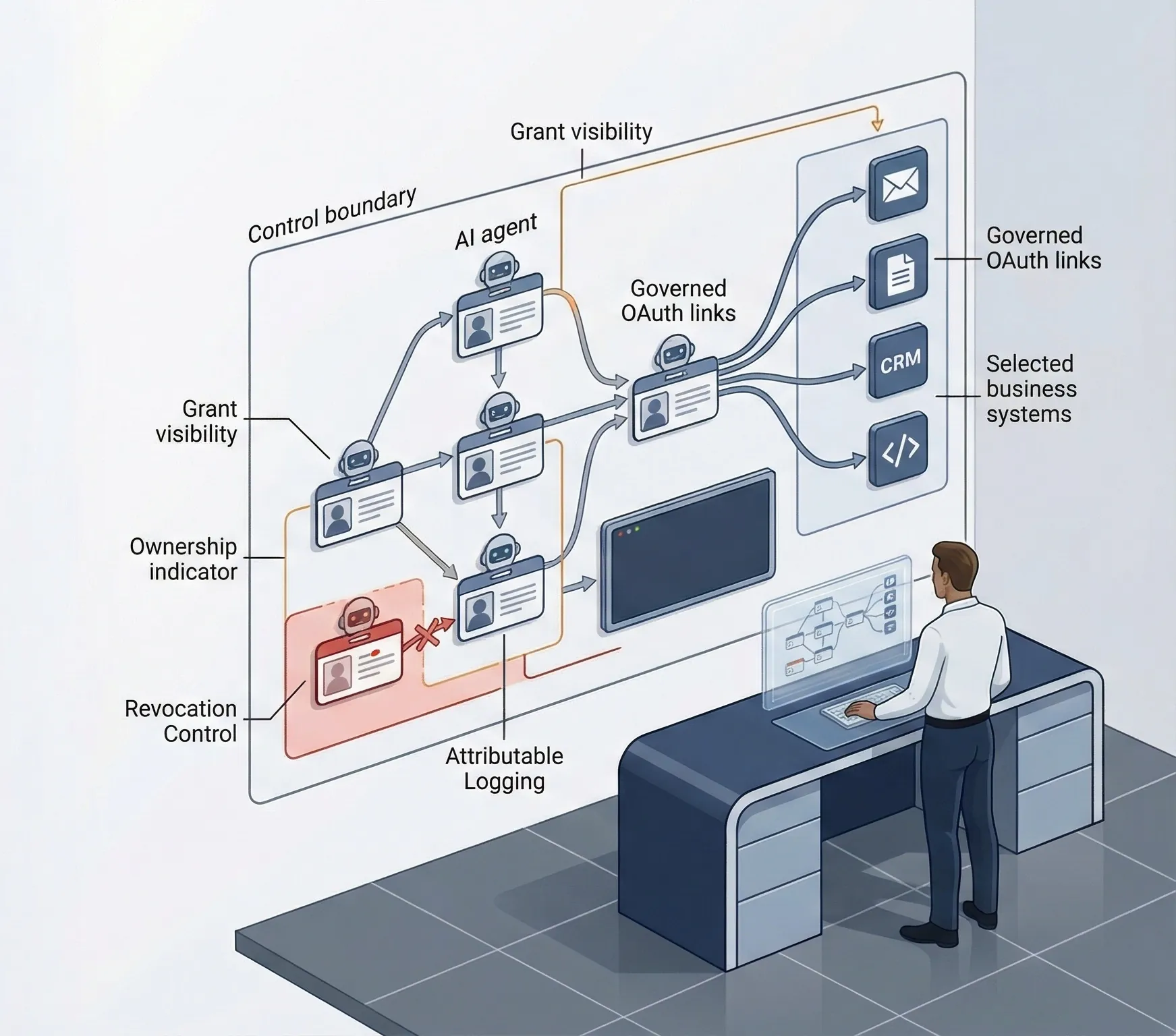
This is a governance visibility screen for AI-agent identities and OAuth-connected access paths. It is not an IAM platform, browser extension, or grant-monitoring product.
- Screens inventory coverage, identity ownership, OAuth-grant visibility, scope discipline, logging quality, revocation readiness, and policy coverage.
- Separates governed visibility from material blind spots before hidden access paths turn into an incident.
- Routes cleanly into AI Controls Starter for inventory and gap analysis, or AI Controls Professional when policy, evidence, incident, and implementation controls are missing.