Agentic AI Governance Operating Model One-Pager
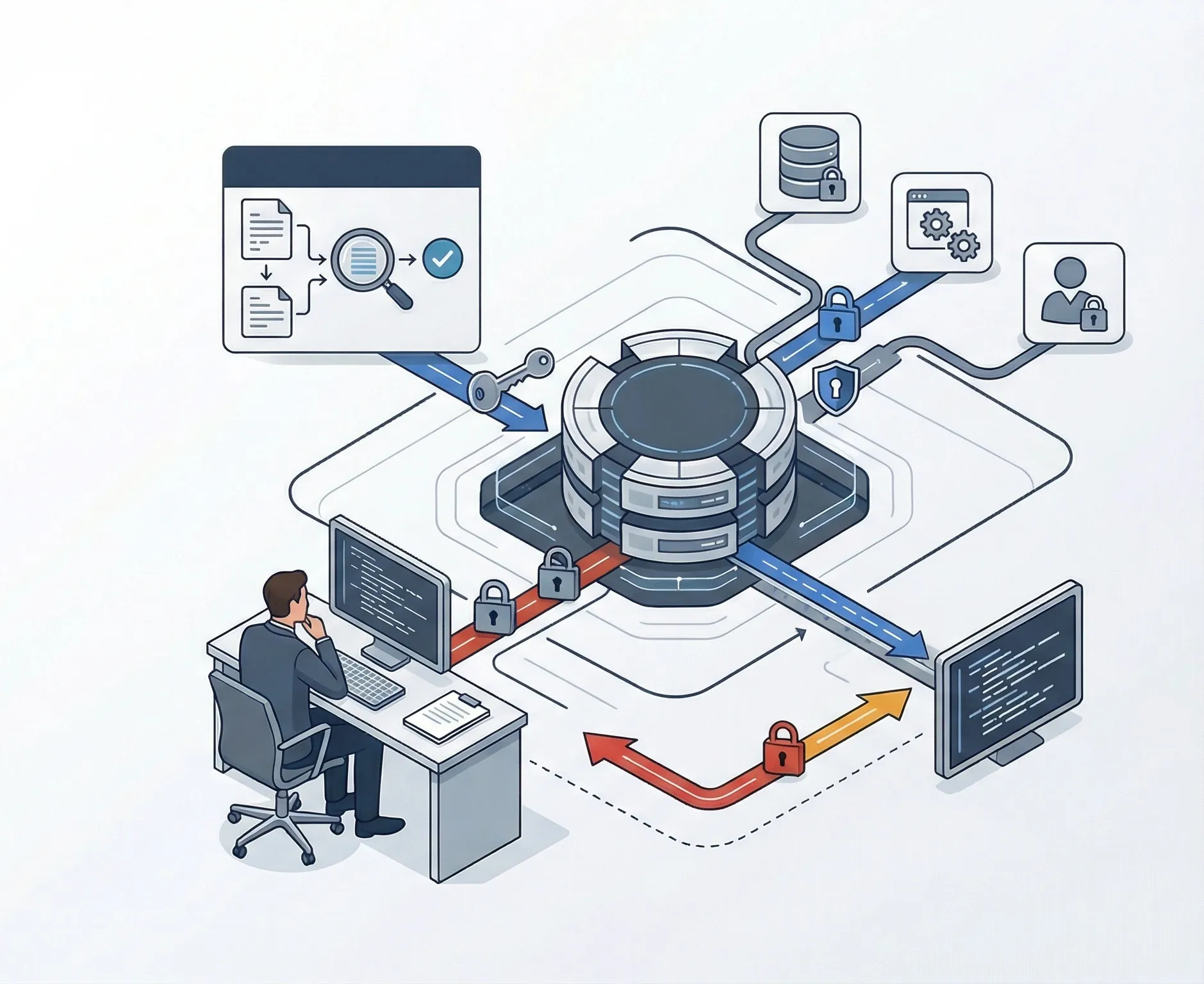
Define governance layers for AI agents, MCP servers, tools, skills, override, kill-switches, evidence, and escalation.
Open artifact page →Decide in under 4 minutes whether an MCP server belongs in sandbox, formal review, or the reject pile.
This is a governance gate for MCP servers. It is not a code scanner, malware verdict, penetration test, or gateway replacement.
This is a governance gate for MCP servers. It is not a code scanner, malware verdict, penetration test, or gateway replacement.
Use this to classify a proposed MCP server as approvable with standard controls, sandbox-only, hold for governance review, or reject.
This section classify MCP approval posture quickly, highlight the biggest gaps, and surface governance gaps and recommend an appropriate implementation path.
This assessment evaluates whether a proposed MCP server is governable from an approval and lifecycle standpoint, including provenance, authorization, testing, credentials, logging, rollback, and approval workflow discipline.
Sandbox only does not automatically mean the server is malicious. It means the evidence and control posture are too weak for normal enterprise rollout.
The missing value is a repeatable MCP approval workflow, retained evidence, lifecycle controls, and policy linkage. That implementation depth sits in AI Controls Professional.
Use AI Controls Professional when the assessment reveals structural control gaps that need policy, procedure, evidence, lifecycle discipline, and implementation ownership.
See the full implementation evidence pack for MCP policy, evidence, lifecycle, and vendor governance.
Use the broader agentic deployment assessment alongside this MCP approval assessment.
Review the tier that includes the MCP Security Governance Checklist and linked implementation assets.
It evaluates maintainer trust, authorization model, tool scope, data exposure, sandbox testing, logging, credential handling, ownership, and approval workflow maturity for a proposed MCP server.
No. It means the evidence or control posture is not strong enough for standard enterprise rollout. The next step is controlled testing and stronger approval evidence, not automatic trust.
Because a server with weak authorization or no reliable rollback path can expand blast radius quickly, especially when it exposes write actions, sensitive data, or shared credentials.
Because experimental MCP adoption is not the same thing as enterprise approval. A formal workflow creates retained evidence, owner accountability, and repeatable decisions across server requests.
No. The assessment runs entirely in the browser. Answers are not stored, synced, or submitted to a server.
MCP approval should not sit in a standalone checklist. Connect approval decisions to an operating model and incident-response artifact for rollback, override, and evidence retention.
Define governance layers for AI agents, MCP servers, tools, skills, override, kill-switches, evidence, and escalation.
Open artifact page →Log agent incidents, classify autonomy failures, document kill-switch decisions, and retain rollback evidence.
Open artifact page →Source and review note: This page was last reviewed on 6 May 2026 against the current Move78 public site baseline and relevant official or authoritative sources where laws, standards, frameworks, cybersecurity controls, product scope, pricing, support policy, or implementation guidance are discussed. It provides operational implementation guidance and product information only; it is not legal advice, tax advice, audit assurance, certification assurance, conformity-assessment advice, buyer-approval assurance, or security assurance. Validate legal, regulatory, contractual, tax, audit, and security decisions with qualified professionals.