What an AIBOM Is
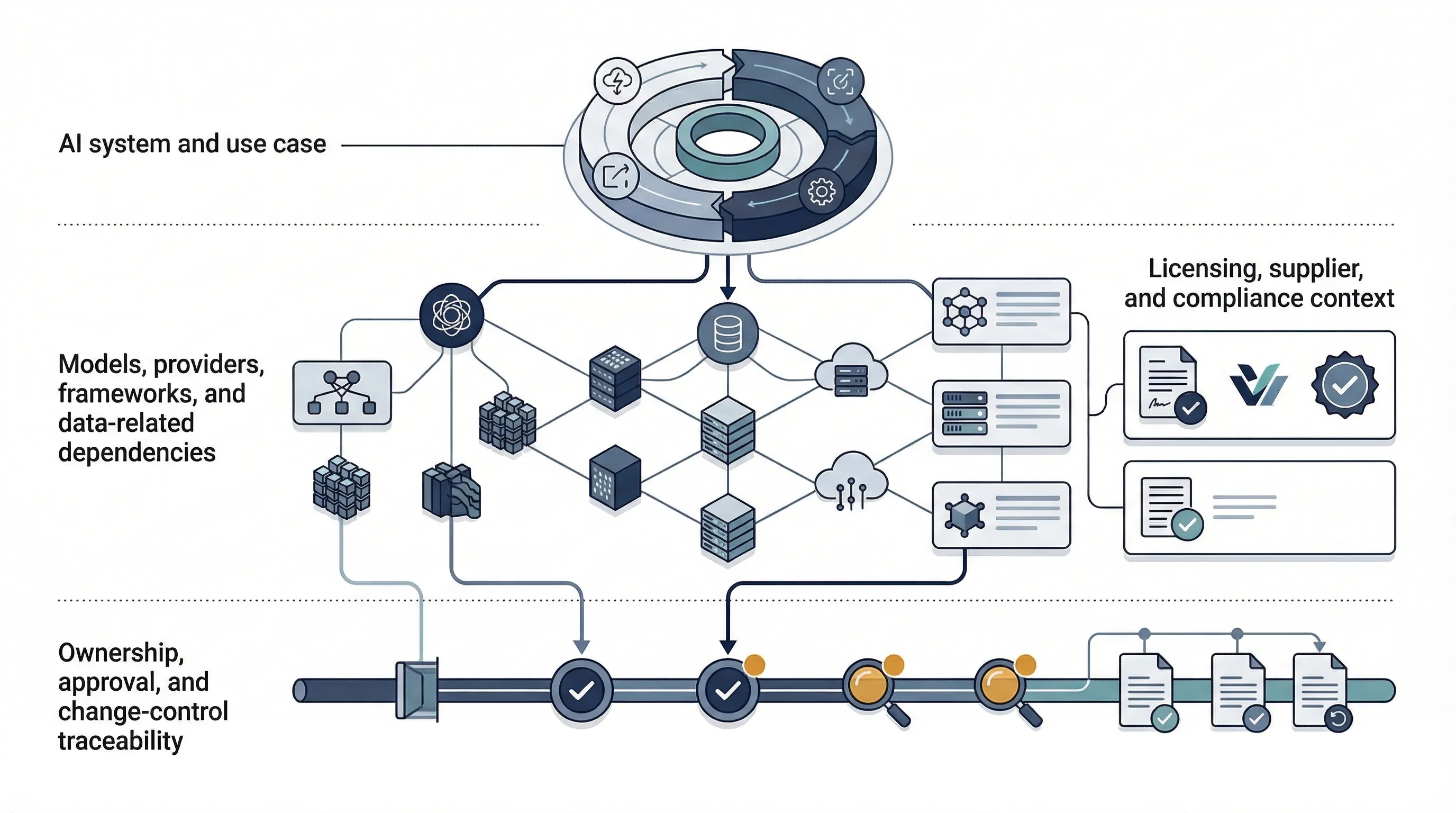
An AIBOM, or AI Bill of Materials, is an AI-focused inventory and traceability artifact. It extends the logic of a software bill of materials into the broader AI system. In practice, that means it can include models, providers, frameworks, libraries, datasets or data-related references, retrieval sources, external APIs, orchestration layers, licenses, compliance notes, and approval history.
The current public AIBOM work is not coming from ISO. It is emerging from open community and standards-adjacent work. OWASP says its AIBOM initiative is advancing open, standardized approaches to AI supply chain transparency and security by operationalizing AIBOM through open-source tooling and measurable completeness assessment. Linux Foundation Research says AI BOM expands beyond SBOM to include algorithms, data collection methods, frameworks and libraries, licensing information, and standards or compliance context. See the OWASP AIBOM initiative and the Linux Foundation AI BOM research.
That framing matters because it keeps the page honest. AIBOM is not law. It is not a certifiable standard. It is not named on ISO's public page for ISO 42001. It is better understood as a practical implementation artifact that helps organizations document what is actually inside an AI system and what dependencies or external conditions could affect risk, compliance, or trust.
Official source links: ISO/IEC 42001 official standard page · OWASP AIBOM initiative · OWASP AIBOM Generator · Linux Foundation AI BOM research
AIBOM vs SBOM vs Model Card vs Datasheet
This section matters because teams blur these artifacts constantly. That creates bad ownership and wasted work. An SBOM is not a model card. A model card is not a dataset datasheet. A vendor questionnaire is not a living technical inventory. An AIBOM overlaps with some of these, but it is broader in the context of an AI system and its dependency chain.
| Artifact | Primary purpose | Scope | Typical owner | Primary use |
|---|---|---|---|---|
| SBOM | Software component transparency | Packages, libraries, software dependencies | Engineering / AppSec | Software supply-chain security |
| AIBOM | AI system dependency and traceability transparency | Models, providers, frameworks, data-related references, retrieval layers, licenses, governance context | Cross-functional | AI inventory, supplier governance, traceability, audit evidence |
| Model card | Model behavior and intended-use communication | Capabilities, limitations, evaluation notes | Model owner / ML team | Explain model-level properties and appropriate use |
| Dataset / datasheet artifact | Data provenance and collection context | Source, collection, composition, intended use, limits | Data owner | Data governance and transparency |
| Vendor questionnaire | Point-in-time assurance gathering | Supplier claims and responses | Procurement / compliance | Due diligence and procurement review |
The clean way to think about it is this. SBOM is software-focused. AIBOM is system-traceability-focused for AI. Model cards and datasheets are supporting artifacts. Vendor questionnaires are external-assurance inputs. None of those alone replaces a living AIBOM.
Why AI Systems Need Supply-Chain Transparency
Normal software inventory logic is not enough for AI systems. A typical AI deployment can include a foundation model, a hosted provider, orchestration code, vector storage, retrieval sources, APIs, prompts, safety filters, fine-tuned variants, and multiple evaluation layers. That is not just a software package tree. It is a dynamic system with technical, contractual, data, and governance dependencies.
Linux Foundation's AI BOM research explicitly supports this broader scope. It says AI BOM expands SBOM by including algorithms, data collection methods, frameworks and libraries, licensing information, and standard-compliance context. OWASP's AIBOM work reinforces the same direction by treating AI supply-chain transparency as something that needs open tooling and measurable completeness rather than informal spreadsheets. See the Linux Foundation report and the OWASP initiative page.
Commercially, that matters for four reasons. Procurement teams want visibility. Customers want traceability. Auditors want evidence. Internal risk owners want to know what changed and where a failure or legal issue came from. Without some form of AIBOM, those questions get answered inconsistently or too late.
Common failure pattern: teams think they have an AI inventory because they know the product name and the model vendor. That is not enough. If you cannot explain the dependencies, retrieval sources, restrictions, and change history, your traceability is weak.
How AIBOM Supports ISO 42001 Implementation
This is the core bridge. ISO's public description of ISO/IEC 42001 says the standard is designed for entities providing or using AI-based products or services and helps organizations manage AI risks while supporting trust and accountability. ISO describes ISO/IEC 42001 as an AI management system standard. That is the right level of abstraction. The public ISO material does not say "build an AIBOM." It does describe the governance and risk-management environment in which an AIBOM becomes useful. See the official standard page and ISO's explanatory article.
| ISO 42001 implementation theme | How AIBOM helps | Example evidence |
|---|---|---|
| AI system inventory | Creates a structured record of what systems and components exist | System register, model/provider list, dependency record |
| Documented information | Provides a living artifact linking technical and governance facts | Versioned AIBOM file, review history, supporting notes |
| Supplier governance | Makes external provider and dependency chains more visible | Provider record, contract notes, licensing restrictions, hosting details |
| Risk assessment inputs | Feeds risk identification with technical and contractual dependencies | Risk register references, evaluation links, dependency-driven risks |
| Operational control | Supports defined ownership and controlled updates | Owner fields, approval status, update cadence |
| Change management | Tracks what changed, when, and why it matters | Change log, model version history, retrieval-source updates |
| Management review evidence | Gives leadership a concrete artifact for system traceability and dependency visibility | Review pack, dashboard extracts, exception notes |
The blunt version is simple. ISO 42001 gives you the management-system frame. AIBOM can become one of the working artifacts that make that frame auditable and usable in practice.
Minimum AIBOM Fields for SMEs
Most SMEs do not need a perfect AIBOM. They need a defensible minimum. Over-engineering the schema before you have basic inventory discipline is the fastest way to stall the whole effort.
| Field | Why it matters |
|---|---|
| System name / ID | Lets you uniquely identify the AI system in the inventory. |
| Business owner | Creates accountability for intended use and approvals. |
| Technical owner | Creates accountability for implementation and updates. |
| Use case / purpose | Anchors the artifact to business context. |
| Model name / version | Tracks what model is actually in use. |
| Model provider / hosting | Captures third-party or regional dependency issues. |
| Model type | Distinguishes LLM, classifier, vision model, recommender, etc. |
| Fine-tuning status | Clarifies whether the model is base or modified. |
| Training / external data dependencies | Documents known upstream data relationships where relevant. |
| Retrieval sources / knowledge bases | Critical for RAG and AI copilots. |
| Frameworks / libraries | Captures technical dependency chain. |
| External APIs / plugins / agents | Documents broader system integration points. |
| Safety filters / moderation | Shows what control layers are present. |
| Prompt / instruction owner | Clarifies who controls model behavior shaping. |
| Licensing / usage restrictions | Reduces IP and misuse surprises. |
| Region / data residency issues | Supports legal and customer assurance questions. |
| Monitoring / evaluation references | Links the AIBOM to testing and oversight artifacts. |
| Last updated date | Shows recency and review discipline. |
| Change history | Supports traceability and incident response. |
| Approval status | Shows whether the system is approved, provisional, or blocked. |
Who Owns the AIBOM Internally
No single function owns all AIBOM content. Product knows the use case. Engineering knows the technical chain. Security or governance knows the control requirements. Procurement or legal often knows the licensing and supplier constraints. Compliance cares about evidence integrity and review cadence. That means one function should own the AIBOM lifecycle, but multiple functions contribute to its quality.
For most SMEs, the recommended pattern is simple. Product or governance owns the artifact lifecycle. Engineering populates technical dependencies. Procurement or legal adds external-provider and restriction fields. Compliance validates that the artifact is reviewable and current. The worst pattern is assuming engineering will handle the whole thing without governance support. That usually produces a technical list, not an assurance artifact.
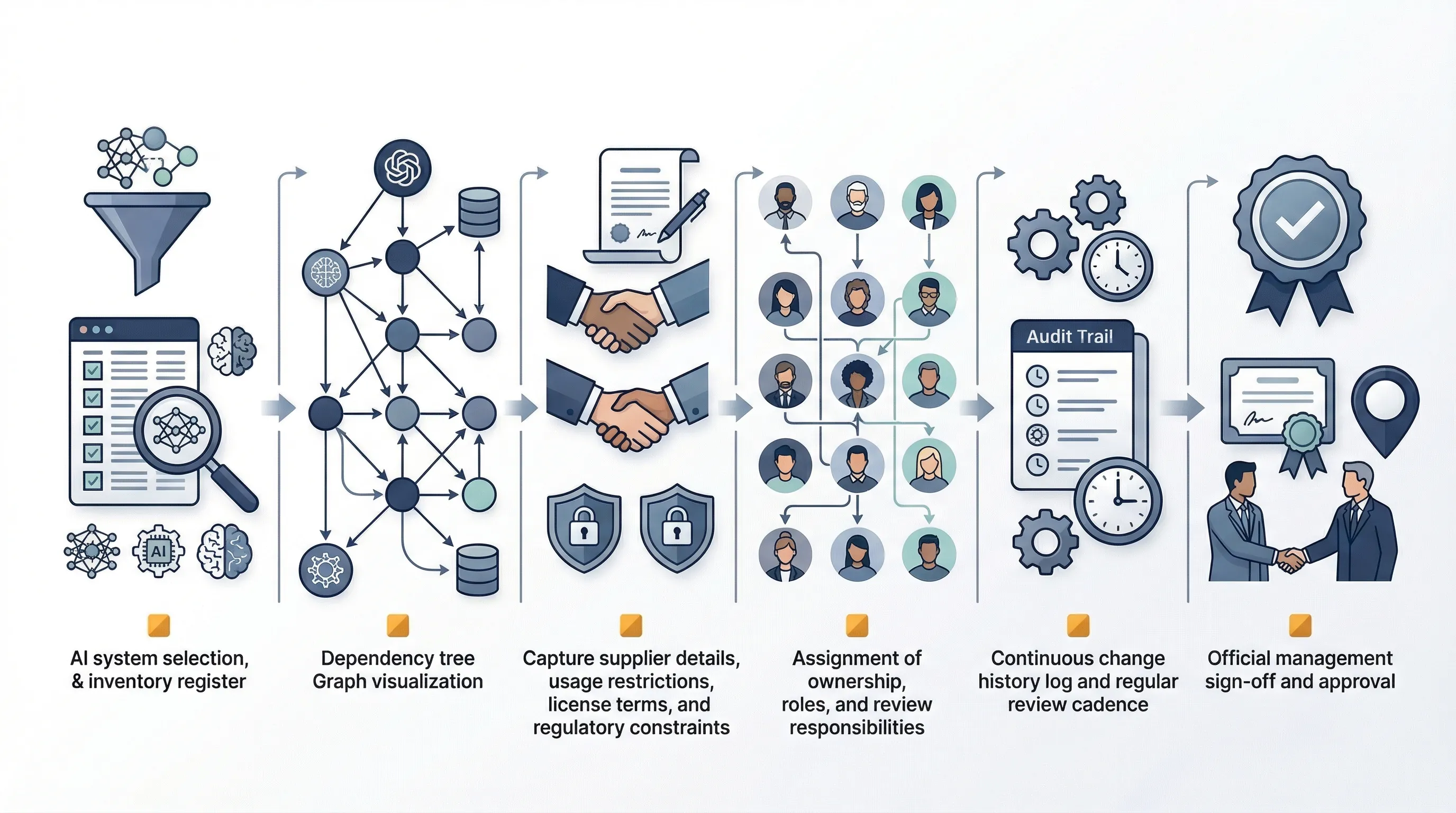
30-Day AIBOM Build Sprint
You do not need a long architecture project. You need a short sprint that gets the minimum viable artifact into place and reviewed.
- Week 1: identify in-scope AI systems, choose the AIBOM template, and assign owners.
- Week 2: populate model, provider, dependency, and use-case fields.
- Week 3: add supplier notes, restrictions, monitoring references, and change history.
- Week 4: validate gaps, approve the baseline, and define update cadence under your ISO 42001 operating model.
The #1 failure reason is almost always the same: teams over-design the schema before they have even finished basic inventory work. Start small. Make it real. Mature later.
Need the templates, not just the concept? AIBOM becomes useful when it is connected to AI inventory, supplier governance, and evidence management. The AI Controls Toolkit (ACT) is designed to help structure those artifacts under a broader ISO 42001 governance model.
Run the free readiness assessment or compare AI Controls Starter and AI Controls Professional.