Agentic AI Incident Log + Shutdown Playbook
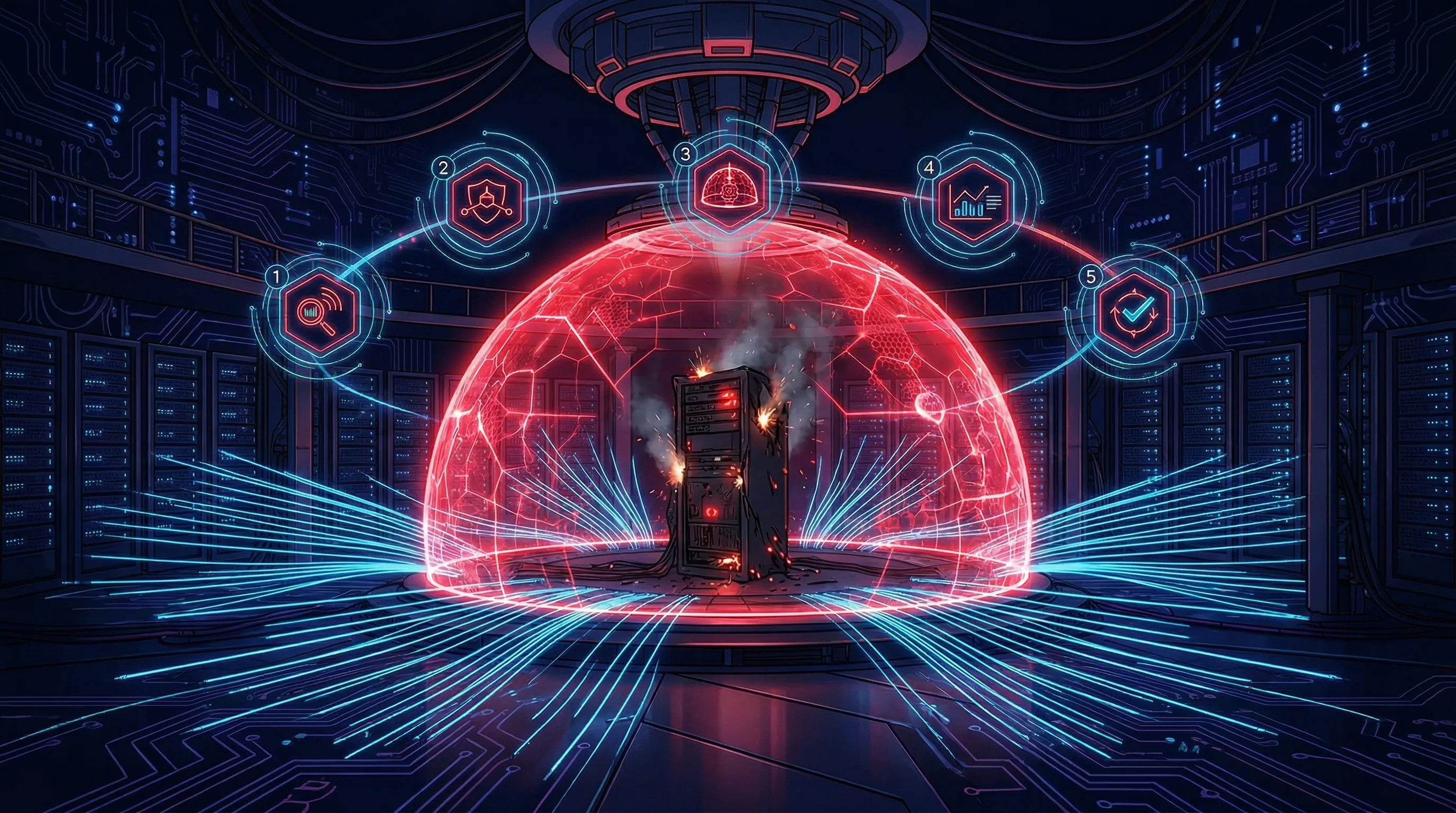
Log agent incidents, classify autonomy failures, document kill-switch decisions, and retain rollback evidence.
Open artifact page →Find out in under 5 minutes whether an OpenClaw incident would be containable or would collapse into improvisation.
This screen is built around shutdown, evidence, credential revocation, rollback, escalation, and board-focused reporting. It does not automate incident handling or produce a live runbook.
This screen is built around shutdown, evidence, credential revocation, rollback, escalation, and board-focused reporting. It does not automate incident handling or produce a live runbook.
Use this to determine whether the organization can disable, investigate, and escalate an OpenClaw compromise with discipline or would still rely on improvisation.
This section classify the governance posture quickly, highlight the biggest gaps, and surface governance gaps and recommend an appropriate implementation path.
It is designed around an OpenClaw compromise or misuse scenario that requires disablement, credential revocation, evidence collection, rollback, escalation, and executive reporting.
A stronger result does not mean OpenClaw incidents are low risk. It means the organization appears more capable of containing, investigating, and escalating one without improvising.
Because a material OpenClaw event can create customer, regulatory, or reputational pressure very quickly. If leadership reporting is absent, the response posture is incomplete.
When the assessment reveals structural control gaps requiring policy, procedure, evidence, and implementation ownership, AI Controls Professional provides the full implementation evidence pack.
See the full implementation evidence pack for incident procedure, evidence, and board-focused reporting.
Start with the broader readiness assessment if the architecture itself is still unclear.
Read the related guide on incident logging, shutdown approvals, and escalation.
It is designed around an OpenClaw compromise or misuse scenario where the team needs to disable the runtime, revoke credentials, preserve evidence, reconstruct events, roll back delegated services, and escalate appropriately.
No. It means the organization appears more capable of containing and investigating an incident. The underlying exposure and business impact may still be significant.
Because without logs and evidence preservation, the organization cannot reconstruct what happened, defend response decisions, or satisfy internal and external scrutiny.
Because a material OpenClaw incident can create contractual, regulatory, and reputational pressure quickly. Response readiness is incomplete if leadership escalation is ad hoc.
No. The assessment runs entirely in your browser. Answers are not stored, synced, or submitted to a server.
If containment readiness is weak, start with an editable incident log and shutdown playbook so escalation, rollback, and evidence retention are not improvised during an incident.
Log agent incidents, classify autonomy failures, document kill-switch decisions, and retain rollback evidence.
Open artifact page →Source and review note: This page was last reviewed on 6 May 2026 against the current Move78 public site baseline and relevant official or authoritative sources where laws, standards, frameworks, cybersecurity controls, product scope, pricing, support policy, or implementation guidance are discussed. It provides operational implementation guidance and product information only; it is not legal advice, tax advice, audit assurance, certification assurance, conformity-assessment advice, buyer-approval assurance, or security assurance. Validate legal, regulatory, contractual, tax, audit, and security decisions with qualified professionals.