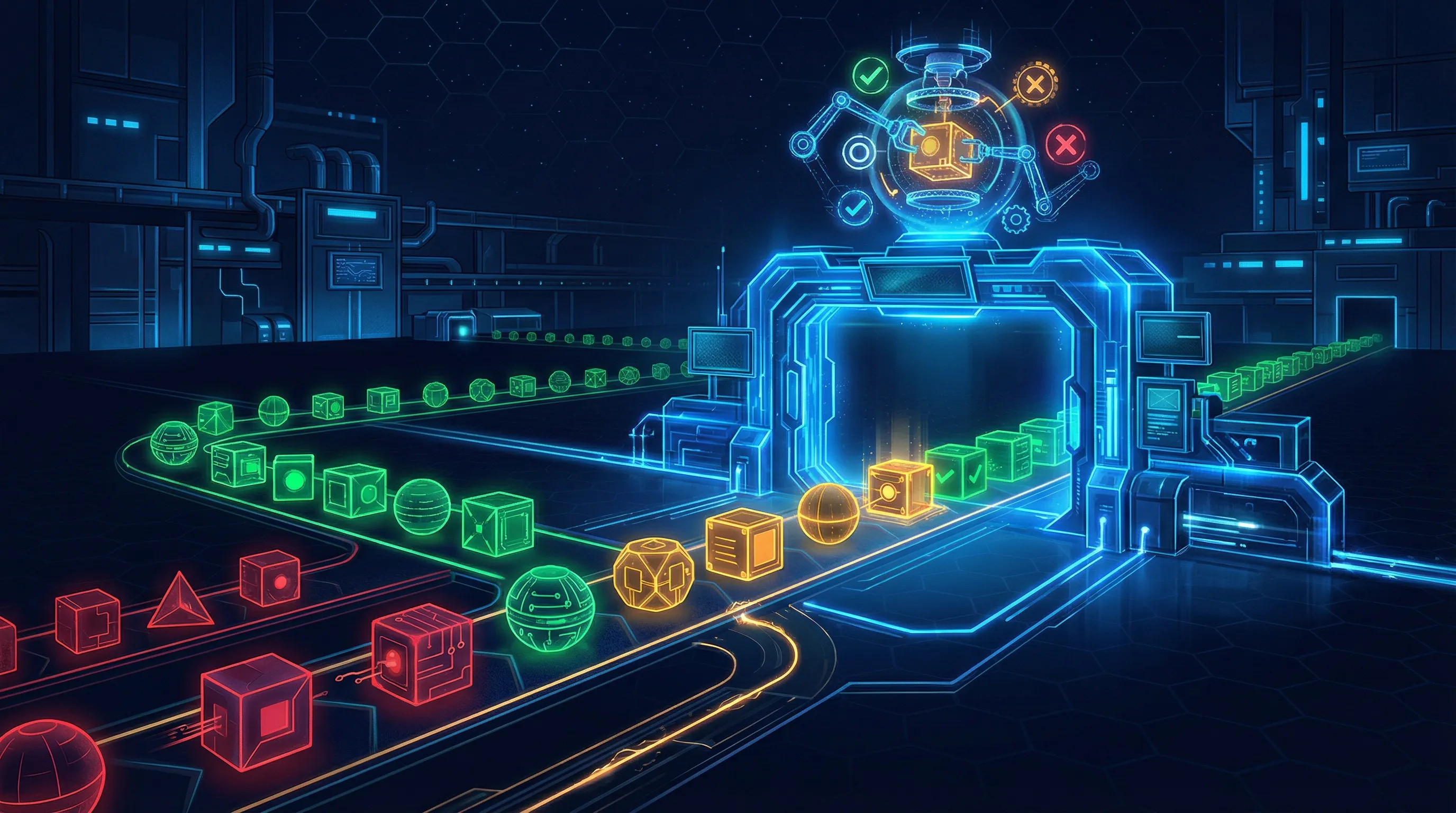
OpenClaw Skill Approval Gate
Decide in under 4 minutes whether an OpenClaw skill belongs in sandbox, production review, or the reject pile.
This is a governance gate for skills, connectors, and MCP-style integrations. It is not a malware scanner, static code analyzer, or signature-based security verdict.
- Screens source trust, provenance, sandbox testing, permission scope, data exposure, rollback, logging, and approval workflow maturity.
- Separates governable skills from opaque skills that should stay out of production.
- Routes directly into AI Controls Professional vendor and agentic governance assets instead of generating a free supplier-review artifact.