Shadow MCP Exposure Check
Find out in under 4 minutes whether unapproved MCP servers are already operating inside your enterprise perimeter.
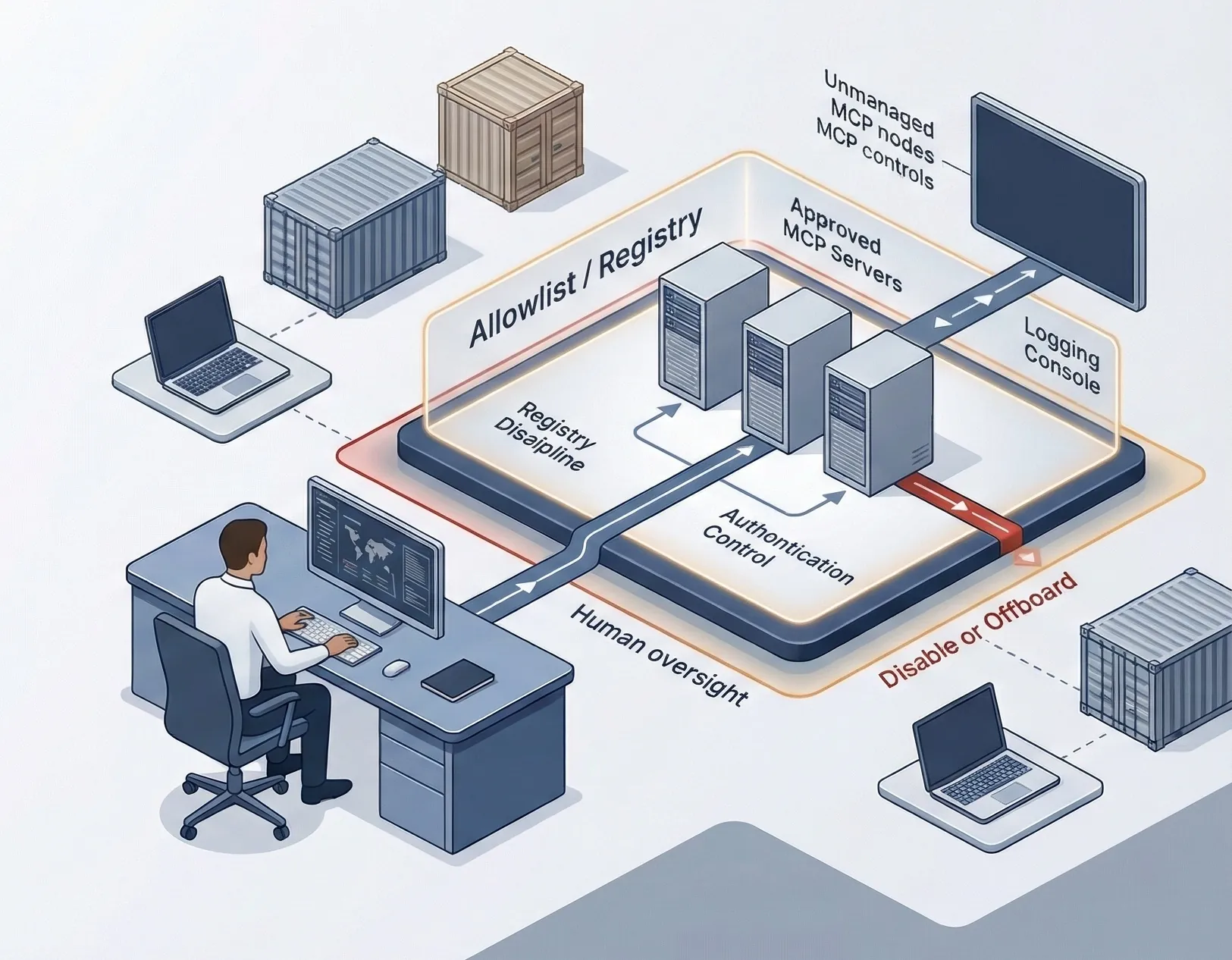
This is a governance visibility screen for unmanaged, local, containerized, or otherwise unapproved MCP deployments. It is not a network scanner, gateway, or telemetry product.
- Screens discovery coverage, registry discipline, local or containerized MCP spread, auth quality, reachable systems, logging, credential handling, disable readiness, and approval workflow maturity.
- Separates controlled MCP footprint from material shadow exposure before hidden deployments turn into a larger governance or incident problem.
- Routes to AI Controls Starter when the immediate need is visibility, inventory, and gap analysis, and escalates to AI Controls Professional when formal governance, evidence, and response controls are missing.