MCP Credential & Scope Governance Check
Find out in under 4 minutes whether MCP servers are running on governable credentials and least-privilege scopes - or on broad, brittle, and poorly owned access.
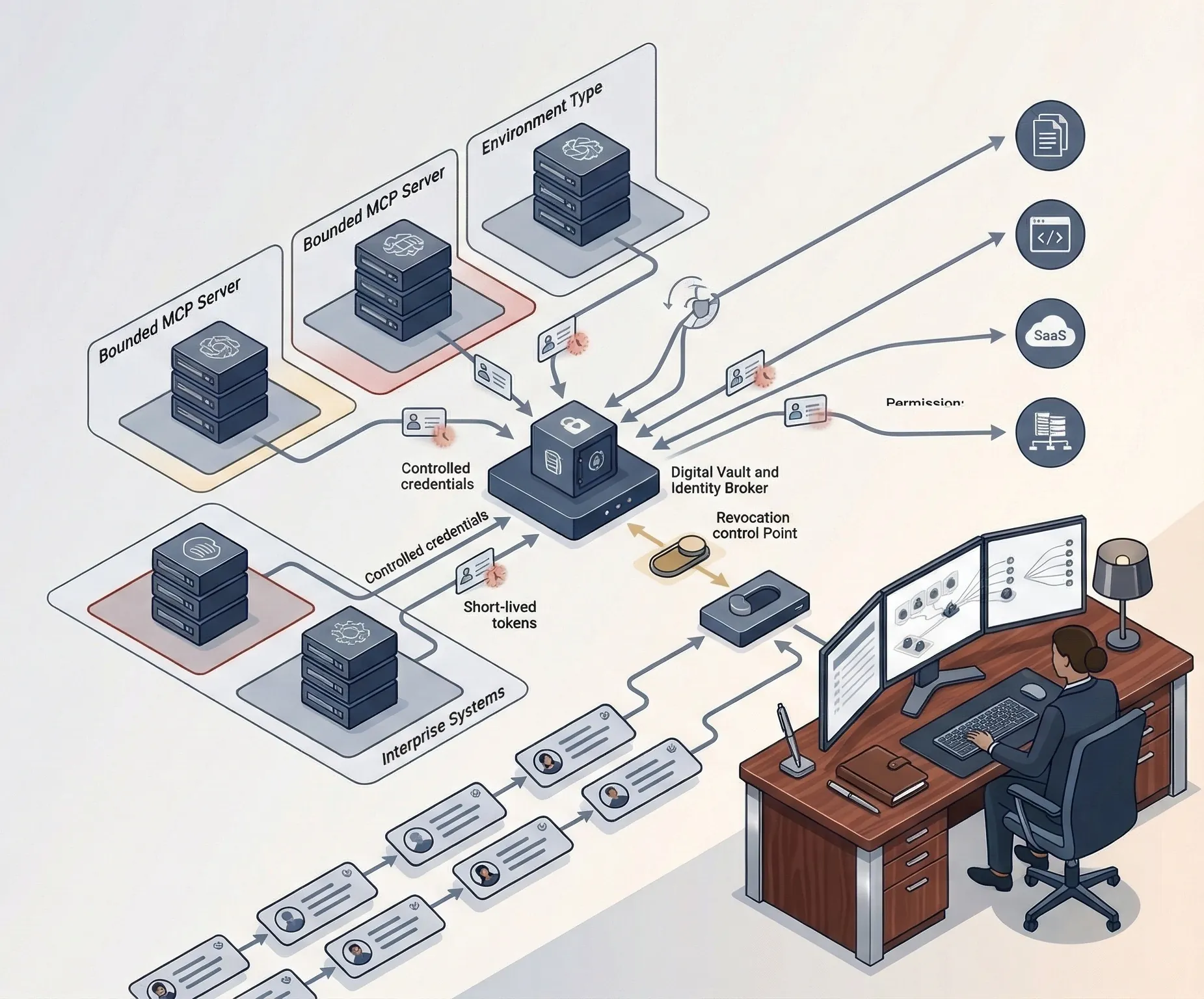
This is a governance assessment for credential issuance, scope discipline, storage, rotation, revocation, and ownership across MCP-connected access paths. It is not a secrets scanner, not a gateway, and not a live token monitor.
- Screens for shared tokens, human credential reuse, broad scopes, plaintext secret handling, weak rotation, and poor revocation readiness.
- Separates bounded credential models from material access exposure before an MCP incident becomes a containment problem.
- Routes directly to AI Controls Professional because the missing value is implementation documentation, evidence, policy, and lifecycle control.